BSD
TrueNAS SCALE adds SMB Clustering and HA in 2nd Major Update
Submitted by Roy Schestowitz on Wednesday 22nd of June 2022 06:35:40 PM Filed under

TrueNAS SCALE 22.02.2 (“Angelfish”) was released today after the previous versions were deployed on over 20,000 active systems. TrueNAS SCALE 22.02.2 includes the completion of SMB clustering and the delivery of High Availability (HA) on TrueNAS M-Series systems. This release is complemented by the new functionality in TrueCommand that provides wizards for creating SMB clusters.
TrueNAS SCALE continues with system count growth at over 100% per quarter since the start of the BETA process in mid 2021. There is widespread adoption by Linux admins and great feedback as TrueNAS SCALE matures.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2940 reads
 PDF version
PDF version
BSD: FreeBSD, OpenBGPD, and NetBSD
Submitted by Roy Schestowitz on Monday 20th of June 2022 05:00:20 AM Filed under
-
Legends start at 1.0! – FreeBSD in 1993 (pt. 1)
In 2017, I wrote a series of articles [1], [2], [3] and [4] on FreeBSD’s famous version 4.11 (and an experiment to use Pkgsrc to get modern software running on it), but I’ve been interested in the history of my operating system of choice for longer than that.
It’s been half a decade since I visited 4.x, my familiarity with FreeBSD has grown further and I finally dare to embark on the adventure to look at the very beginning. I had originally thought about doing this in a VM. However while dusting off an old laptop of mine to test 13.1-BETA releases on, I thought that I might give ancient FreeBSD a shot on that machine. It is an Acer TravelMate 272XC laptop that I got in 2003 (see dmesg at the bottom if you want to know more). It is not the oldest machine that I still have, but it is the last one with a working floppy drive!
So I would simply install FreeBSD 1.0, mess with it a little and then write an article about it. Nothing too complicated, should be done in a couple of hours on a weekend! Except it turned out to be… just a little more involved.
-
OpenBGPD 7.4 released
[...] However, the release notes may be found in this mailing list post from June 14th, 2022: https://marc.info/?l=openbsd-announce&m=165521316007652&w=2
-
Is FreeBSD a Real UNIX?
Lets get back to the computing world. Can you officially name FreeBSD a UNIX? No. That is because Open Group company owns copyright to the ‘UNIX’ term. You can call it only a UNIX-like system … but that does not mean its not UNIX. You just can not call it like that because of the lawyers.
NetBSD team also gave good example with their ‘duck’ explanation – https://mollari.netbsd.org/about/call-it-a-duck.html – available here.
Apple paid $100 000 to call their Mac OS X (now macOS) system a UNIX officially.
-
Advanced Programming in the UNIX Environment
This document will guide you through the setup of a NetBSD VM using UTM on an Apple M1 to perform all your course work on. Please follow these steps as shown; if you run into problems or have questions, please send them to the class mailing list.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2277 reads
 PDF version
PDF version
Help Us Celebrate FreeBSD Day All Week Long
Submitted by Roy Schestowitz on Sunday 19th of June 2022 01:50:09 PM Filed under

As you may know, June 19th has been declared FreeBSD Day, and we hope you’ll join us in honoring the Project’s pioneering legacy and continuing impact on technology. This year, the Foundation is celebrating all week long.
- 1 comment
 Printer-friendly version
Printer-friendly version- Read more
- 2247 reads
 PDF version
PDF version
New FreeBSD Core Team Elected
Submitted by Roy Schestowitz on Saturday 18th of June 2022 05:08:29 PM Filed under
Dear FreeBSD Community, The FreeBSD Project is pleased to announce the completion of the 2022 Core Team election. Active committers to the project have elected your Twelfth FreeBSD Core Team. Baptiste Daroussin (bapt) Benedict Reuschling (bcr) Ed Maste (emaste) Greg Lehey (grog) John Baldwin (jhb) Li-Wen Hsu (lwhsu) Emmanuel Vadot (manu) Tobias C. Berner (tcberner) Mateusz Piotrowski (0mp) Let's extend our gratitude to the outgoing Core Team members for their service over the past two years (in some cases, many more) : George V. Neville-Neil (gnn) Hiroki Sato (hrs) Warner Losh (imp) Kyle Evans (kevans) Mark Johnston (markj) Scott Long (scottl) Sean Chittenden (seanc) The Core Team would also like to thank Allan Jude (allanjude) for running a flawless election. To read about the responsibilities of the Core Team, refer to https://www.freebsd.org/administration.html#t-core Regards, Moin (bofh), Core Team Secretary
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2139 reads
 PDF version
PDF version
GhostBSD 22.06.15 ISO is now available
Submitted by Roy Schestowitz on Saturday 18th of June 2022 05:06:33 PM Filed under
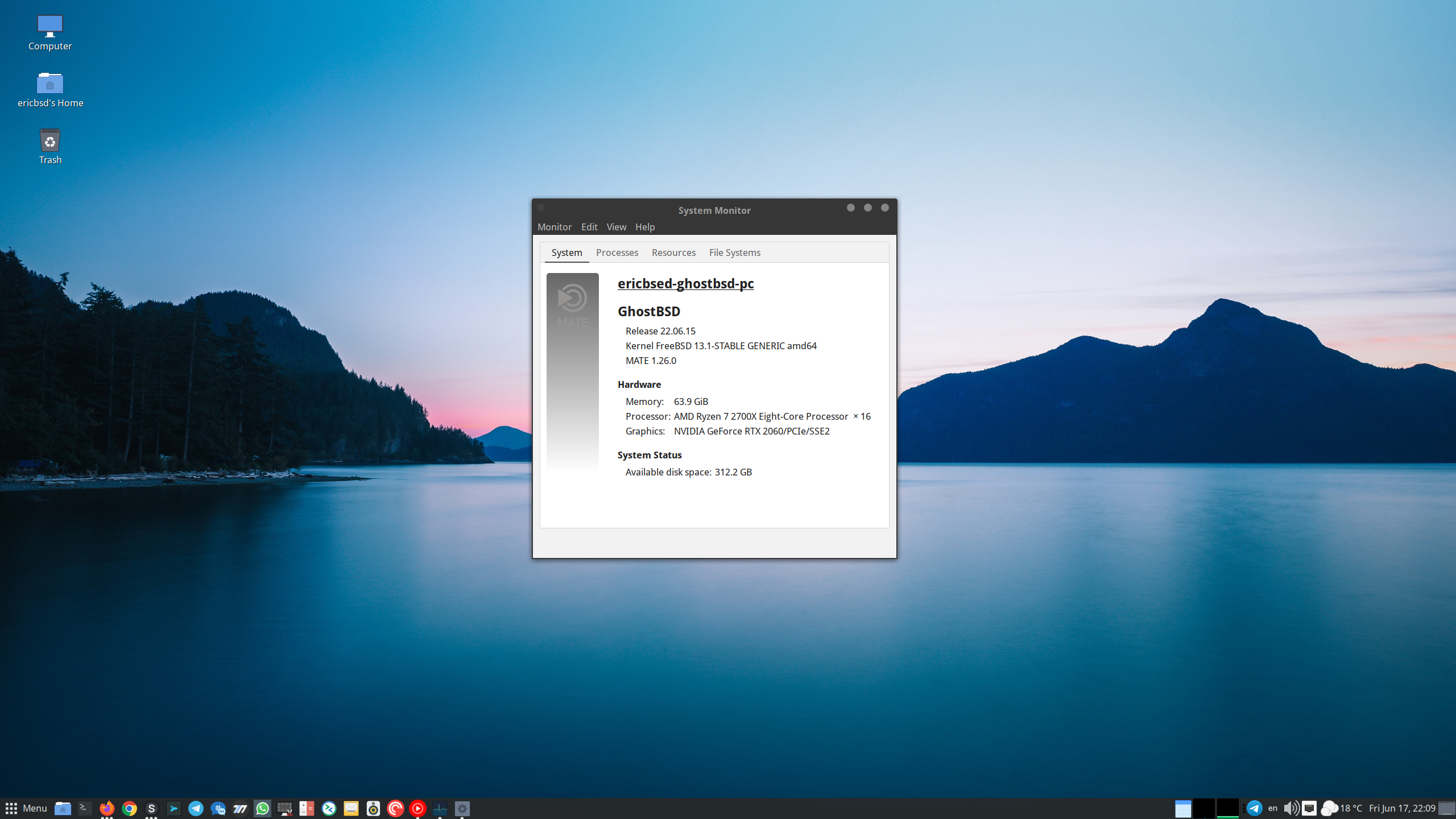
After five months, this new ISO is more than overdue. It contains many bug fixes, security fixes, feature improvements, software updates, and OS updates. For details, see the changelog below.
- 1 comment
 Printer-friendly version
Printer-friendly version- Read more
- 2130 reads
 PDF version
PDF version
BSD Leftovers
Submitted by Roy Schestowitz on Saturday 18th of June 2022 10:15:41 AM Filed under
-
BSD Now 459: NetBSD Kernel benchmark
This week’s BSD Now is depressingly honest in the title; no puns. Along with the normal links, there’s a Beastie Bit this week for Networks From Scratch.
-
Two versions, both right
An interesting thought: since HAMMER2 is intended to be a multi-master file system, it has to figure out – and quickly – which is the most up to date versions of any given file. That means you could have multiple versions of a file existing at the same time until that decision is made. That wouldn’t be visible from a user perspective.
-
Using Netgraph for FreeBSD’s bhyve Networking
FreeBSD’s bhyve hypervisor offers support for virtual networks connections. Beginning with FreeBSD13, bhyve also supports a netgraph backend for its virtual network devices.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2417 reads
 PDF version
PDF version
Audiocasts/Shows: Enterprise Linux Security, Linux Action New, and BSD Now
Submitted by Roy Schestowitz on Thursday 16th of June 2022 03:31:03 PM Filed under


-
Enterprise Linux Security Episode 32 - MySQL for Everyone! - Invidious
Are you a fan of MySQL? What if we told you that there's an infinite supply of it online, right out in the open?! It's literally as bad as it sounds! In this episode, Jay and Joao discuss how over 3.6 million MySQL instances are publicly available, as well as other forms of unintended public access.
-
Linux Action News 245
We get the details behind Thunderbird acquiring K-9 Mail, share the best new features of Plasma 5.25, check-in on Ubuntu's RISC-V development status, and discuss Photoshop coming to Linux via the web.
-
BSD Now 459: NetBSD Kernel benchmark
Evaluating FreeBSD CURRENT for Production Use, Time Machine-like Backups on OpenBSD, FreeBSD on the Graviton 3, Compiling the NetBSD kernel as a benchmark, Network Management with the OpenBSD Packet Filter Toolset from BSDCan 2022, Hardware Detection & Diagnostics for New FreeBSD Users, and more
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2443 reads
 PDF version
PDF version
OpenBGPD 7.4 released
Submitted by Roy Schestowitz on Wednesday 15th of June 2022 08:23:17 AM Filed under
We have released OpenBGPD 7.4, which will be arriving in the OpenBGPD directory of your local OpenBSD mirror soon.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2415 reads
 PDF version
PDF version
FreeBSD Foundation: Foundation Elects New Officers, Interviews Outgoing Board Members
Submitted by Roy Schestowitz on Sunday 12th of June 2022 02:12:58 PM Filed under
On May 31, 2022 The FreeBSD Foundation held its Annual Board Meeting. An important part of the meeting includes electing Board Officers and Directors for the following 12 month period. We’re pleased to announce the FreeBSD Foundation 2022-2023 Board includes:
President, Treasurer, and Founder: Justin T. Gibbs
Vice President: Andrew Wafaa
Secretary: Kevin Bowling
Director: Cat Allman
Director: Hiroki Sato
Director: Robert N.M. Watson
Assistant Secretary: Deb Goodkin
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2129 reads
 PDF version
PDF version
MidnightBSD 2.2
Submitted by Roy Schestowitz on Saturday 11th of June 2022 01:17:09 PM Filed under

I’m happy to announce the availability of MidnightBSD 2.2 for amd64 and i386. This release focused on updating third party software in the base system and some smaller enhancements.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2272 reads
 PDF version
PDF version
More in Tux Machines
- Highlights
- Front Page
- Latest Headlines
- Archive
- Recent comments
- All-Time Popular Stories
- Hot Topics
- New Members
digiKam 7.7.0 is released
After three months of active maintenance and another bug triage, the digiKam team is proud to present version 7.7.0 of its open source digital photo manager. See below the list of most important features coming with this release.
|
Dilution and Misuse of the "Linux" Brand
|
Samsung, Red Hat to Work on Linux Drivers for Future Tech
The metaverse is expected to uproot system design as we know it, and Samsung is one of many hardware vendors re-imagining data center infrastructure in preparation for a parallel 3D world.
Samsung is working on new memory technologies that provide faster bandwidth inside hardware for data to travel between CPUs, storage and other computing resources. The company also announced it was partnering with Red Hat to ensure these technologies have Linux compatibility.
|
today's howtos
|







.svg_.png)
 Content (where original) is available under CC-BY-SA, copyrighted by original author/s.
Content (where original) is available under CC-BY-SA, copyrighted by original author/s.

Recent comments
47 weeks 1 day ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 3 days ago
47 weeks 3 days ago
47 weeks 3 days ago