Hardware
Raspberry Pi Zero Prints Giant Pictures with Thermal Receipt Printer
Submitted by Roy Schestowitz on Monday 27th of June 2022 09:59:07 AM Filed under

It’s no secret that thermal receipt printers can print much more than receipts, but this Raspberry Pi project, created by a maker known as -PJFry- on Reddit, has taken the idea to a new extreme. With the help of a Raspberry Pi Zero, they’ve coded an application to print huge, poster-sized images (opens in new tab) one strip at a time on their thermal printer.
Inspiration for this project came from similar online projects where users print large-scale images using regular printers or thermal printers like the one used in this project. In this case, however, -PJFry- coded the project application from scratch to work on the Pi Zero. It works by taking an image and breaking it into pieces that fit across the width of the receipt printer and printing it one strip at a time. Then, these strips can be lined up to create a full-sized image.
It is the only microelectronics project we can find that -PJFry- has shared, but it’s clear they have a great understanding of our favorite SBC to craft something this creative from scratch. According to -PJFry-, the project wasn’t created for efficiency but more for fun as a proof of concept. The result is exciting and provides an artistic take on the Raspberry Pi’s potential.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 26397 reads
 PDF version
PDF version
Devices With GNU/Linux and Hardware Hacking
Submitted by Roy Schestowitz on Monday 27th of June 2022 08:39:59 AM Filed under
-
Introducing ESP32-C5: Espressif’s first Dual-Band Wi-Fi 6 MCU
ESP32-C5 packs a dual-band Wi-Fi 6 (802.11ax) radio, along with the 802.11b/g/n standard for backward compatibility. The Wi-Fi 6 support is optimised for IoT devices, as the SoC supports a 20MHz bandwidth for the 802.11ax mode, and a 20/40MHz bandwidth for the 802.11b/g/n mode.
-
Compulab’s new IoT gateway is based on NXP’s i.MX.8M processor and runs on Linux, MS Azure IoT and Node RED [Ed: Compulab should shun spyware from Microsoft. Bad neighbourhood.]
The IOT-GATE-IMX8PLUS is an IoT gateway made by Compulab that is based on the NXP i.MX.8M Plus System on Chip (SoC) for commercial or industrial applications. The device features dual GbE ports, Wi-Fi6/BLE 5.3 support, LTE 4G, GPS and many optional peripherals.
Compulab’s new IoT gateway provides support for two processor models, the C1800Q and the C1800QM. Both come with a real time processor but only the C1800QM includes the AI/ML Neural Processing Unit.
-
Want A Break From Hardware Hacking? Try Bitburner
If you ever mention to a normal person that you’re a hacker, and they might ask you if you can do something nefarious. The media has unfortunately changed the meaning of the word so that most people think hackers are lawless computer geniuses instead of us simple folk who are probably only breaking the laws meant to prevent you from repairing your own electronics. However, if you want a break, you can fully embrace the Hollywood hacker stereotype with Bitburner. Since it is all online, you don’t even have to dig out your hoodie.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 24491 reads
 PDF version
PDF version
Raspberry Pi and Raspberry Pi Pico Projects
Submitted by Roy Schestowitz on Sunday 26th of June 2022 12:16:32 PM Filed under
-
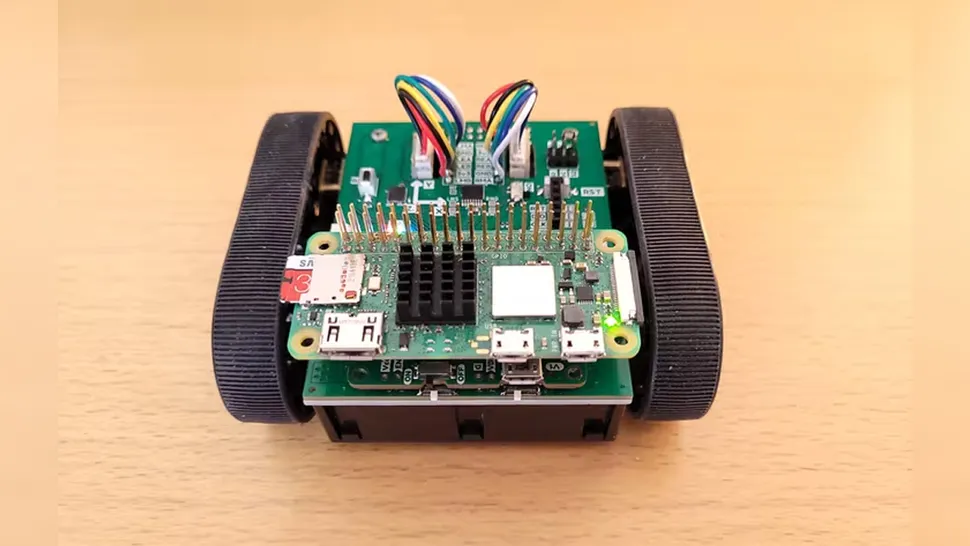
Tiny Raspberry Pi Zero 2 W Robot Made For Robot Sumo | Tom's Hardware
The Raspberry Pi in robotics is a smart mix—but what happens if the kit you ordered doesn’t support the Pi? You get creative like maker and developer WallComputer, of course! In this Raspberry Pi Zumo project, they've converted the classic Pololu Arduino Zumo kit to support the latest Raspberry Pi Zero 2 W.
This tiny robot uses tank-like treads to get around, which provide the traction needed for Sumo robots designed to push each other around. Traditionally this type of robot is controlled by an Arduino Uno, but this version uses both a Raspberry Pi Zero 2 W and an STM32 microcontroller with a little help from a couple of custom PCBs. To see how much has been modified, take a look at the original product listing for the Zumo kit over at Pololu’s website. This modification was not only necessary to use the Pi, but also to add additional features like a rechargeable battery pack.
-
Best Raspberry Pi Deals 2022 | Tom's Hardware
With more than 40 million units sold and a powerful community of makers and fans behind it, Raspberry Pi is more than a single-board computer; it's a huge platform with an even bigger ecosystem behind it. Whether you want to build your own robot, create an A.I.-powered security camera, or just set up a simple computer for programming and web surfing, the Pi is for you.
-
Raspberry Pi Pico Drives $10 Nintendo 64 Flash Cart | Tom's Hardware
We love retro gaming on the Raspberry Pi but there’s nothing quite like retro gaming with a Raspberry Pi. Instead of running an emulator on a Pi, this Raspberry Pi Pico Nintendo 64 cart project, created by maker and developer Konrad Beckmann, is using the Raspberry Pi Pico to host a ROM that runs on the original Nintendo 64 console.
I built a working Nintendo 64 flash cart with a Raspberry Pi Pico, a breakout board and some extra flash for less than $10.It boots Super Mario 64. Can't wait to optimize, improve and add more features to it!Lots of stuff left before it's ready for general users though. pic.twitter.com/C1qVaTTfHiJune 22, 2022
-
Raspberry Pi Pico Detects Gamma Rays in Open Spectroscopy Project | Tom's Hardware
There are many useful things you can do with a Raspberry Pi Pico (opens in new tab), as our listing of the best Raspberry Pi Projects (opens in new tab) underlines. However, here’s one we admit we’d never thought of: detecting radiation. Physicist Matthias Rosezky, AKA Nuclear Phoenix (opens in new tab), whose work has also been covered by Hackaday (opens in new tab), has written up a detailed account of building a DIY gamma-ray spectrometer in IEEE Spectrum (opens in new tab).
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2455 reads
 PDF version
PDF version
Motion Detection with PIR and Raspberry PI: HC-SR501 wiring and Python Code
Submitted by Roy Schestowitz on Sunday 26th of June 2022 11:49:39 AM Filed under


Projects involving motion detection actions require a reliable way to run their code when an object movement happens. One of the most common solutions to accomplish this task is by the HC-SR501 PIR sensor with Raspberry PI.
In this tutorial, I’m going to show you how to connect and use a PIR with Raspberry PI computer boards using Python.
What is a PIR
A PIR (Passive InfraRed, sometimes named “PID” as “Passive Infrared Detector”) sensor is an electronic device able to measure the infrared (IR) light radiating from objects. The term passive means that the PIR module doesn’t radiate energy for detection purposes: it only detects infrared radiation emitted by or reflected from objects.
It can make your project aware if a generic movement happened in its range of view, but it can’t give more information (like, for example, who, where and how many the object moved).
You can find a more detailed description of how the PIR works from the following Glolab PIR page.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2698 reads
 PDF version
PDF version
Mixtile Edge 2 Kit mini PC/IoT gateway supports an external 20Ah battery pack
Submitted by Roy Schestowitz on Sunday 26th of June 2022 11:47:04 AM Filed under

Mixtile Edge 2 Kit is a mini PC/IoT edge computer powered by a Rockchip RK3568 quad-core Cortex-A55 processor coupled with up to 4GB RAM and 32GB flash that features a 12V SATA + SMBUS port that allows the insertion of a 20Ah battery pack lasting up to 12 hours for locations where power may be intermittent.
[...]
Software support includes Android 11 with Linux containers (Mixtile OS) like initially announced for the Blade 3 but based on customers’ feedback, I’ve read Mixtile changed their mind for the latter and now plans to make a proper Linux image without Android running in the background.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 3520 reads
 PDF version
PDF version
Where to Find Free Schematic Drawing Software for Arduino, Raspberry Pi, and Other SBCs
Submitted by Roy Schestowitz on Saturday 25th of June 2022 06:21:43 PM Filed under


Circuit diagrams play a vital role in the design process for any electronics project. They give you the chance to plan your circuit before you make it and can save a lot of time and effort. But how can you make circuit diagrams to improve your designs?
We have gathered some of the web's most popular free schematic drawing software options for Arduino, Raspberry Pi, and other SBCs to make your choice easier.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 3938 reads
 PDF version
PDF version
Best Linux laptops of 2022
Submitted by Roy Schestowitz on Saturday 25th of June 2022 02:16:51 PM Filed under



While Mac and Windows computers tend to dominate the discussions, Linux laptops deserve your consideration. While making the switch may involve a learning curve, Linux machines will reward you with a stable and secure operating system that offers a free, private, open-source platform. Some manufacturers still make it difficult to install Linux products on their laptops, although there are workarounds available to make almost any laptop run the OS. To avoid the potential problems of installing your own software, purchase one of the best Linux laptops that come ready to go right out of the box.
Buying a laptop with Linux pre-installed also ensures that future software updates from the manufacturer will be supported. You won’t need to tinker with the operating system to ensure good performance. The following Linux laptops can provide solid options for professional machines, school computers, and even personal laptops for tinkering and coding.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 4247 reads
 PDF version
PDF version
Bambu Lab X1 - A color 3D Printer with LIDAR and AI for improved accuracy, ease of use (Crowdfunding)
Submitted by Rianne Schestowitz on Saturday 25th of June 2022 07:28:27 AM Filed under


3D printing can be time-consuming and challenging, and even today, it’s still not as easy as using a photocopier, but the team at Bambu Lab has taken it upon itself to make a better, easier-to-use 3D printer with the X1 color 3D printer combining LIDAR and AI technology to level the bed, calibrate the prints, and detect anomalies.
The Bambu Lab X1 3D printer supports up to 16 colors, is making removing support easier with snap-away material or dissolvable filament, can handle PC and PA-CF filaments beyond the traditional PLA and PETG filaments, manage up to 500 mm/s prints, and provides better prints with features such as active vibration compensation. Oh, and you don’t need to assemble it, since it comes fully assembled and ready to use out of the box.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 3850 reads
 PDF version
PDF version
A RISC-V laptop or mini PC with Rockchip RK3588-class performance may be coming soon
Submitted by Rianne Schestowitz on Friday 24th of June 2022 11:11:47 AM Filed under




The hardware and software specifications of the device will depend on the answers to the survey. First, it’s not sure we’ll get a RISC-V laptop since respondents will first be asked for the type of product, so we may end up with a fairly powerful RISC-V mini PC or/and SBC first instead.
You’ll also be asked for your use case, preferred Linux operating system (Ubuntu, Debian, Fedora, others), desktop environment, as well as software packages you may need such as LibreOffice, Chromium or Firefox browsers, GIMP, Thunderbird, and so on. As a side note, they’ll select 5 winners from the respondents and send them on VisionFive RISC-V SBC with the results announced sometime in July on RVSpace community. If you don’t need to enter the draw, you do not need to leave your name and email to complete the survey.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 4581 reads
 PDF version
PDF version
Open Hardware/Modding leftovers
Submitted by Roy Schestowitz on Friday 24th of June 2022 06:10:46 AM Filed under

-
Answering Questions about the PetaPi
The first thing I tried was upgrading the firmware on the HBAs—four Broadcom 9405W-16i cards. I noticed they were on version 5, which was from November 2017. A lot has changed in the past five years, and HBAs and RAID cards see a lot of active development to fix bugs, optimize throughput, etc., since they basically run their own on-chip OS.
-
Proof of Life: I Still Have Something to Say
In fact the only downside of the Dev One is the shitty Realtek wireless card it ships with. If you buy one of these, I strongly suggest you crack it open and switch out the wifi card for an Intel AX200 or AX201. It is 100% worth it, especially as the machine does not come with an ethernet port. Despite the 5850U processor in the Dev One having a TDP that is 1/3rd of the TDP of the 4800H in the Pulse laptop, performance is about the same. Battery life is worse, but the Pulse has a 90+ watt hour battery whereas the HP has a 53 watt hour battery. Nevertheless I can get 6 to 8 hours on it with no problem, which is more than enough for me.
In addition, the screen on the Dev One is beautiful. I honestly was scared shitless of buying this device because it only comes with a glossy screen and I have been using matte screens for so long that I wasn't sure how well I would be able to adapt. Nevertheless these fears proved to be baseless as the screen is phenomenal. In addition the laptop ships in a single configuration which is fine as the RAM, Storage and Wifi are all upgrade-able (provided you have a Torx T5 screwdriver) and yes I upgraded all of them. The free shipping is great as its overnight shipping. I literally ordered this thing last Monday and got it the following afternoon.
-
How use both Hue bulbs and Lutron switches in your smart home
The downside of these and other smart bulbs is that they need to be powered on for voice or app control. And if you have automations for those lights, they need power for your smart home to run those automations.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 3647 reads
 PDF version
PDF version
More in Tux Machines
- Highlights
- Front Page
- Latest Headlines
- Archive
- Recent comments
- All-Time Popular Stories
- Hot Topics
- New Members
digiKam 7.7.0 is released
After three months of active maintenance and another bug triage, the digiKam team is proud to present version 7.7.0 of its open source digital photo manager. See below the list of most important features coming with this release.
|
Dilution and Misuse of the "Linux" Brand
|
Samsung, Red Hat to Work on Linux Drivers for Future Tech
The metaverse is expected to uproot system design as we know it, and Samsung is one of many hardware vendors re-imagining data center infrastructure in preparation for a parallel 3D world.
Samsung is working on new memory technologies that provide faster bandwidth inside hardware for data to travel between CPUs, storage and other computing resources. The company also announced it was partnering with Red Hat to ensure these technologies have Linux compatibility.
|
today's howtos
|







.svg_.png)
 Content (where original) is available under CC-BY-SA, copyrighted by original author/s.
Content (where original) is available under CC-BY-SA, copyrighted by original author/s.

Recent comments
47 weeks 1 day ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 3 days ago
47 weeks 3 days ago
47 weeks 3 days ago